You will also need to install a tool (bridge utils) which doesn't come pre-installed in Kali. No big deal-
apt-get install bridge-utils
Objectives
The whole process can be broken down into the following steps-
- Finding out about the access point (AP) you want to imitate, and then actually imitating it (i.e. creating another access point with the same SSID and everything). We'll use airmon-ng for finding necessary info about the network, and airbase-ng to create it's twin.
- Forcing the client to disconnect from the real AP and connecting to yours. We'll use aireplay-ng to deauthenticate the client, and strong signal strength to make it connect to our network.
- Making sure the client doesn't notice that he connected to a fake AP. That basically means that we have to provide internet access to our client after he has connected to the fake wireless network. For that we will need to have internet access ourselves, which can be routed to out client.
- Have fun - monitor traffic from the client, maybe hack into his computer using metasploit.
PS: The first 3 are primary objectives, the last one is optional and not a part of evil twin attack as such. It is rather a man in the middle attack. Picture credits : firewalls.com
Information Gathering - airmon-ng
To see available wireless interfaces-
iwconfig
To start monitor mode on the available wireless interface (say wlan0)-
airmon-ng start wlan0To capture packets from the air on monitor mode interface (mon0)
airodump-ng mon0After about 30-40 seconds, press ctrl+c and leave the terminal as is. Open a new terminal.
Creating the twin
Now we will use airbase-ng to create the twin network of one of the networks that showed up in the airodump-ng list. Remember, you need to have a client connected to the network (this client will be forced to disconnect from that network and connect to ours), so choose the network accordingly. Now after you have selected the network, take a note of it's ESSID and BSSID. Replace them in given code-
airbase-ng -a <BSSID here> --essid <ESSID here> -c <channel here> <interface name>If you face any problems, a shorter code will be-
airbase-ng --essid <name of network> mon0
 Remove the angular brackets (< & >) and choose any channel that you want. Also, the BSSID can be randomly selected too, and doesn't have to match with the target. The interface would be mon0 (or whatever is the card you want to use) . The only thing identical about the twins has to be their ESSIDs (which is the name of the network). However, it is better to keep all parameters same to make it look more real. After you are done entering the parameters and running the command, you'll see that airbase turned your wireless adapter into an access point.
Remove the angular brackets (< & >) and choose any channel that you want. Also, the BSSID can be randomly selected too, and doesn't have to match with the target. The interface would be mon0 (or whatever is the card you want to use) . The only thing identical about the twins has to be their ESSIDs (which is the name of the network). However, it is better to keep all parameters same to make it look more real. After you are done entering the parameters and running the command, you'll see that airbase turned your wireless adapter into an access point.Note : We will need to provide internet access to our client at a later stage. Make sure you have a method of connecting to the net other than wireless internet, because your card will be busy acting like an AP, and won't be able to provide you with internet connectivity. So, either you need another card, or broadband/ADSL/3G/4G/2G internet.
 |
| Man in the middle attack : Pic Credits: owasp.net |
Telling the client to get lost
Now we have to ask the client to disconnect from that AP. Our twin won't work if the client is connected to the other network. We need to force it to disconnect from the real network and connect to the twin.
For this, the first part is to force it to disconnect. Aireplay will do that for us-
aireplay-ng --deauth 0 -a <BSSID> mon0 --ignore-negative-one
.png)
The 0 species the time internal at which to send the deauth request. 0 means extremely fast, 1 would mean send a packet every 1 seconds, 2 would mean a packet every 2 seconds, and so on. If you keep it as 0, then your client would be disconnected in a matter of seconds, so fire up the command, and press ctrl+c after a few seconds only. Note that the deauth is sent on broadcast, so all the clients (not just one) connected to the network will disconnect. Disconnecting a specific client is also possible.
Not the real one, but why the fake one
Even after being disconnected from the real AP, the client may choose to keep trying to connect to the same AP a few more times, instead of trying to connect to ours. We need to make our AP stand out, and for that, we need more signal strength. There are 2 ways to do that-- Physically move closer to the client.
- Power up your wireless card to transmit at more power.
iwconfig wlan0 txpower 27Here 27 is the transmission power in dBm. Some cards can't transmit at high power, and some can transmit at extremely high power. Alfa cards usually support upto 30dBm, but many countries don't allow the card to transmit at such powers. Try changing 27 to 30 and you'll see what I mean. In Bolivia, however, you can transmit at 30dBm, and by changing the regulatory domain, we can overcome the power limitation.
iw reg set BO
iwconfig wlan0 txpower 30It is strongly advised to not break laws as the transmission limits are there for a reason, and very high power can be harmful to health (I have no experimental evidence). Nevertheless, the client should connect to you if your signal strength is stronger than that you the real twin.
Note : If you are unable to get your client to connect to you, there is another option. You can leave him with no options. If you keep transmitting the deauth packets continuously (i.e. don't press ctrl+c after the client has disconnected), he will have no choice but to connect to you. However, this is quite an unstable situation, and the client will go back to the real twin as soon as it gets the chance.
Give the fake AP internet access
Now we need to provide internet access to the fake AP. This can be done in various ways. In this tutorial, we will consider that we have an interface x0 which has internet connectivity. Now, if you are connected to net via wireless, replace x0 with wlan1 or wlan0, a 3G modem will show up as ppp0. Nevertheless, you just have to know which interface is providing you with internet, and you can route the internet access to your client.
Interfaces
- x0 - This has internet access
- at0 - This is create by airbase-ng (wired face of the wireless access point). If you can somehow give internet access to at0, then the clients connected to your fake wireless network can connect to the net.
- evil - This is an interface that we will create, whose job will be to actually bridge the networks.
Creating evil
We will use Bridge control utility provided by Kali, brctl. Execute the following code-
brctl addbr evilThis will create the bridge. Now we have to specify which two interfaces have to be bridged-
brctl addif evil x0
brctl addif evil at0We can assign an IP to the interfaces and bring them up using-
ifconfig x0 0.0.0.0 up
ifconfig at0 0.0.0.0 upAlso bring up the evil interface (the interfaces aren't always up by default so we have to do this many times)
ifconfig evil upNow to auto configure all the complicated DHCP settings, we'll use dhclient
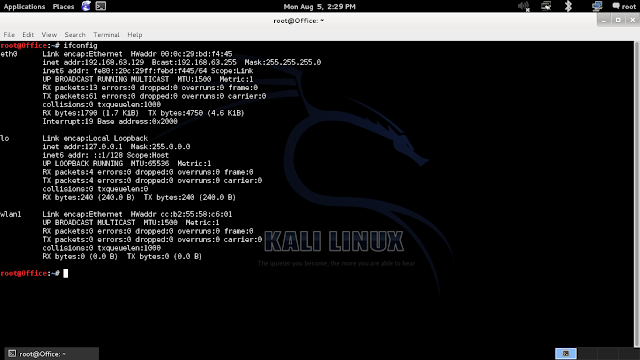
dhclient3 evil &Finally, all the configurations have been completed. You can execute ifconfig and see the results, which will show you all the interfaces you have created.
Officially, the evil twin attack is complete. The client is now connected to your fake network, and can use the internet pretty easily. He will not have any way to find out what went wrong. However, the last objective remains.
Have fun
Now that the client is using the internet via our evil interface, we can do some evil stuff. This actually comes under a Man In The Middle attack (MITM), and I'll write a detailed tutorial for it later. However, for the time being, I will give you some idea what you can do.
 Sniffing using Wireshark
Sniffing using Wireshark
Now all the packets that go from the user to the internet pass through out evil interface, and these packets can be monitored via wireshark. I won't teach you how to use it here, since it is a GUI tool. You can take a look at their website to get an idea on how to use wireshark. Pic credits: The picture on the right has been directly taken from their website.